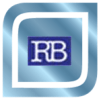
Artificial Intelligence (AI) has moved from experimental technology to a central pillar of enterprise strategy. Across industries, organizations are redefining how they operate, invest, and compete by embedding AI into core processes. Today’s leading companies are not merely adopting AI tools; they are designing comprehensive AI strategies that align technology with business outcomes, workforce capabilities, and long-term competitiveness.
This article explores how organizations are approaching AI strategy, where they are investing, how they are integrating AI into operations, and how emerging technologies are shaping future business performance.
1. AI as a Strategic Business Imperative
Over the past few years, AI has shifted from isolated innovation projects to enterprise-wide transformation programs. Surveys indicate that a majority of companies now use AI in some capacity, primarily in decision support, analytics, and customer interactions. (arXiv)
This shift reflects a growing recognition that AI is not just an IT capability but a strategic asset capable of reshaping industries.
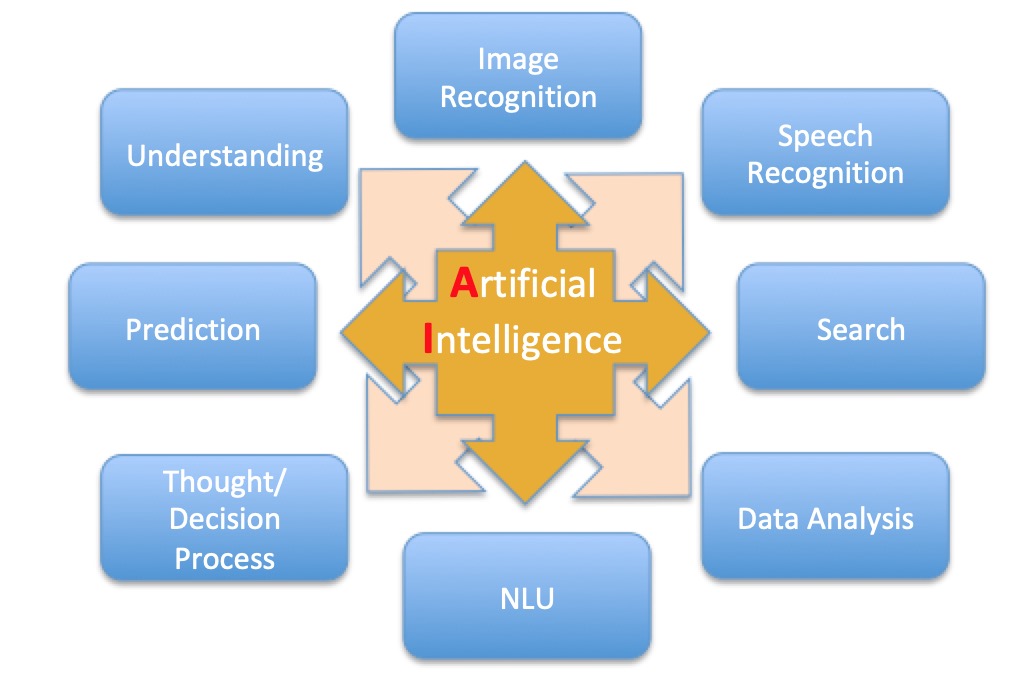
Many organizations now structure their AI strategy around three key principles:
- Business value alignment – selecting AI use cases that directly support revenue growth or cost reduction.
- Data infrastructure development – building robust data platforms that support large-scale AI deployment.
- Workforce transformation – training employees to collaborate effectively with AI systems.
A notable example is enterprise consulting firm Accenture, which has adopted an “AI-first” strategy. Employees are expected to use AI tools as part of their daily work, and the company has invested heavily in AI training for leadership and staff. (Business Insider)
This reflects a broader trend: organizations increasingly view AI literacy as a core skill for the modern workforce.
2. AI Investment Priorities Across Industries
Corporate investment in AI is rising rapidly, with companies allocating a growing portion of technology budgets toward AI-related initiatives. Some estimates suggest that organizations may dedicate around 20% of technology spending to AI by the mid-2020s, reflecting its importance for productivity and innovation. (Mezzi)
However, investment priorities differ significantly by industry.
Financial Services
Financial institutions were among the earliest adopters of AI due to their heavy reliance on data. AI applications in this sector include:
- Fraud detection
- Risk assessment
- Algorithmic trading
- Personalized financial services
Platforms that use AI-driven analytics can analyze massive financial datasets in real time, enabling more accurate forecasting and decision-making. (Mezzi)
Companies such as Ant Group illustrate this trend. The company launched AI-driven healthcare and financial services platforms using large language models to expand its digital ecosystem and reach millions of users. (Wikipedia)
Manufacturing
Manufacturing companies are heavily investing in AI for operational efficiency. The most common applications include:
- Predictive maintenance
- Quality control using computer vision
- Supply chain optimization
Approximately 77% of manufacturers now use AI solutions, with many reporting reduced downtime and improved operational reliability. (Netguru)
These technologies allow factories to predict equipment failures before they occur, saving significant costs and improving productivity.
Retail and Consumer Industries
Retailers use AI primarily to enhance customer experience and optimize operations. Key applications include:
- Personalized recommendations
- AI-powered chatbots
- Inventory optimization
- Demand forecasting
Retailers that deployed AI chatbots during peak shopping periods reported measurable increases in online conversion rates. (Mezzi)
Startups such as Duvo.ai are developing AI workforce platforms that automate repetitive operational tasks across retail systems, reducing manual work and improving efficiency. (Wikipedia)
3. From Experimentation to Operational Integration
Many organizations initially approached AI through small pilot projects or experimentation. However, leading enterprises are now focusing on scaling successful AI applications into core business operations.
A clear example is Johnson & Johnson, which tested nearly 900 AI use cases during its early experimentation phase. The company later discovered that only about 10–15% of those use cases generated the majority of value, prompting a shift toward a more targeted AI strategy focused on drug discovery, supply chains, and sales support tools. (The Wall Street Journal)
This highlights a key lesson in enterprise AI adoption: the real value often comes from a relatively small number of high-impact applications.
Another example comes from logistics giant FedEx, which is integrating AI agents into multiple operational areas, including network planning, marketing, and customs processes. The company expects AI to support over half of its core operations in the coming years. (The Wall Street Journal)
Such initiatives demonstrate how AI is evolving from a support tool into a central operational capability.
4. The Technology Stack Behind Enterprise AI
Successful AI deployment requires more than algorithms. Organizations are investing in an ecosystem of technologies that enable scalable AI implementation.
Key components include:
Data Platforms
Enterprise data platforms provide the infrastructure needed to collect, process, and analyze large datasets.
Examples include:
- AI platforms such as IBM’s watsonx for model development and governance.
- Cloud-based platforms like Google Cloud’s Vertex AI for building and deploying machine-learning models. (The News Strike)
These platforms help organizations bring AI applications from experimental prototypes into production environments.
Automation and AI Agents
AI agents are increasingly used to automate complex workflows and decision-making processes. These agents can:
- Coordinate business processes
- Analyze operational data
- Execute actions across enterprise systems
Voice AI systems from companies like SoundHound AI, for example, enable conversational interfaces across automotive systems, retail ordering platforms, and enterprise customer service. (Wikipedia)
This technology represents a shift toward autonomous digital workers capable of collaborating with human employees.
5. Emerging Technologies Reshaping Business Performance
Several emerging technologies are accelerating the impact of AI across industries.
Generative AI
Generative AI models, including large language models, are transforming knowledge work by automating content creation, coding, and research tasks.
These systems allow organizations to:
- accelerate innovation cycles
- automate design processes
- generate new product ideas
Researchers note that generative AI is reshaping economic systems by enabling new forms of automation and creativity across industries. (arXiv)
AI-Driven Robotics
AI-powered robotics is transforming manufacturing and logistics. For example, robotics companies are collaborating with AI developers to create robots that can train in virtual environments before deployment in real-world settings. (Financial Times)
This approach significantly reduces development costs and speeds up deployment.
Autonomous AI Agents
Autonomous AI agents capable of performing multi-step tasks are expected to become a major enterprise technology trend. These systems can:
- coordinate workflows
- monitor operations
- optimize decision processes
As these technologies mature, organizations may rely on AI agents as digital collaborators rather than simple tools.
6. Organizational Challenges and Governance
Despite its promise, implementing AI at scale presents significant challenges.
Common obstacles include:
- Data governance and privacy concerns
- Integration with legacy systems
- Workforce resistance or skills gaps
- Ethical and regulatory considerations
Research shows that organizational factors—such as leadership alignment and change management—often determine AI success more than technical capability. (arXiv)
Effective AI governance frameworks therefore focus on transparency, accountability, and responsible use of algorithms.
7. The Future of AI-Driven Business Performance
Looking ahead, AI is expected to become a fundamental component of competitive strategy. Organizations that successfully integrate AI into their operations are likely to benefit from:
- faster decision-making
- improved operational efficiency
- new digital products and services
- enhanced customer experiences
As AI technologies continue to evolve, businesses will increasingly operate within human-AI hybrid environments, where machines augment human capabilities rather than replace them.
Companies that treat AI as a long-term strategic capability—rather than a short-term technology experiment—will be best positioned to thrive in the emerging digital economy.
8. Future Trends in Artificial Intelligence and Business Transformation
Looking ahead, artificial intelligence is expected to become even more deeply embedded in business strategy and operational execution. The next wave of AI adoption will not simply focus on efficiency improvements but will fundamentally reshape how organizations operate, innovate, and compete. Several emerging trends are likely to define the future of AI-driven enterprises.
8.1 AI as a Core Layer of Enterprise Infrastructure
AI is gradually becoming a foundational layer within enterprise technology stacks, similar to how cloud computing evolved over the past decade. Instead of being implemented as separate tools, AI capabilities will increasingly be integrated directly into enterprise platforms, software systems, and business workflows.
Major enterprise technology companies such as Microsoft, Google, and Amazon are embedding AI into productivity suites, development platforms, and cloud services. This integration allows organizations to leverage AI without building complex infrastructure from scratch.
For example, AI assistants embedded into enterprise software are already helping employees automate document creation, analyze datasets, and streamline routine administrative tasks. As these tools become more sophisticated, AI will function as an always-available “digital colleague” supporting human decision-making.
8.2 Autonomous AI Agents and Digital Workforces
One of the most transformative developments in AI is the rise of autonomous AI agents. These systems are capable of performing complex multi-step tasks with minimal human supervision.
Unlike traditional automation systems that follow predefined rules, AI agents can interpret context, make decisions, and coordinate across multiple systems. This allows them to handle activities such as:
- Managing supply chain logistics
- Conducting financial analysis
- Performing customer service interactions
- Coordinating internal workflows
Companies are already experimenting with digital workforces made up of AI agents that collaborate with human employees. In logistics and operations, organizations such as FedEx are exploring AI agents to support planning, customer service, and operational optimization.
In the future, organizations may operate with hybrid teams composed of both human employees and AI agents working together.
8.3 Industry-Specific AI Models
Another important trend is the development of industry-specific AI models. Early AI systems were designed as general-purpose tools, but businesses increasingly require specialized models trained on industry-specific datasets.
These models are tailored for domains such as:
- Healthcare diagnostics
- Financial risk modeling
- Manufacturing optimization
- Legal research
For example, pharmaceutical companies are using AI to accelerate drug discovery by analyzing biological datasets and identifying potential compounds. Firms such as Johnson & Johnson are investing heavily in AI-driven research platforms that significantly shorten the drug development cycle.
Industry-focused AI models are expected to produce greater accuracy, reliability, and regulatory compliance compared to general-purpose models.
8.4 AI-Driven Innovation and Product Development
AI is also transforming how organizations design and develop new products. By analyzing large datasets and running simulations, AI systems can generate design alternatives, identify market opportunities, and optimize engineering processes.
In sectors such as automotive and aerospace, AI-powered design tools are helping engineers explore thousands of potential product configurations in a fraction of the time previously required.
Automotive companies such as Tesla are using AI extensively in both vehicle software development and manufacturing optimization. The company’s AI systems support autonomous driving capabilities while also improving factory production processes.
As generative design and simulation technologies evolve, AI will increasingly act as a creative partner in product development.
8.5 Human-AI Collaboration and Workforce Transformation
Rather than replacing human workers entirely, the future of AI will likely involve deep collaboration between humans and intelligent systems.
Organizations are already redefining job roles to incorporate AI tools into daily workflows. Employees are being trained to work alongside AI systems that can:
- analyze complex data
- generate insights
- automate repetitive tasks
Consulting firms such as Accenture have begun requiring employees to use AI tools as part of their daily work environment, signaling a shift toward AI-augmented workplaces.
This transformation will require continuous workforce reskilling and the development of new capabilities such as:
- AI literacy
- data interpretation
- human-AI collaboration management
Companies that invest in workforce development will likely gain a competitive advantage in the AI-driven economy.
8.6 Responsible AI and Regulatory Frameworks
As AI becomes more powerful and widely deployed, governments and organizations are placing greater emphasis on responsible AI practices.
Key areas of focus include:
- transparency of AI decision-making
- protection of personal data
- prevention of algorithmic bias
- ethical deployment of autonomous systems
Regulatory initiatives such as the EU Artificial Intelligence Act are establishing legal frameworks for how AI systems should be developed and deployed. Similar regulatory discussions are taking place in many countries worldwide.
Organizations will increasingly need to implement governance structures that ensure AI systems are fair, transparent, and accountable.
8.7 AI and the Next Phase of Digital Transformation
Ultimately, AI represents the next phase of digital transformation. While earlier waves of digital transformation focused on digitizing processes and moving operations to the cloud, AI enables organizations to extract deeper insights and automate complex decision-making.
Companies that successfully harness AI will likely achieve significant advantages in areas such as:
- operational efficiency
- customer personalization
- innovation speed
- strategic decision-making
However, the benefits of AI will not be realized automatically. Organizations must combine technological investment with cultural change, leadership commitment, and long-term strategic vision.
Conclusion and Closing Persepctive
Artificial intelligence is rapidly reshaping the way organizations operate, compete, and innovate. Across industries, companies are developing strategic AI roadmaps, investing in scalable platforms, and integrating AI into everyday business processes.
The organizations that succeed will be those that combine technological investment with organizational transformation – aligning AI with business strategy, workforce development, and responsible governance.
As emerging technologies such as generative AI, robotics, and autonomous agents mature, AI will increasingly define the future of enterprise performance and competitive advantage.
The future of business will be increasingly shaped by intelligent technologies that augment human capabilities and redefine organizational performance. Artificial intelligence is no longer a speculative technology; it is becoming a core component of modern enterprise strategy.
Organizations that embrace AI thoughtfully—integrating it into operations, investing in talent development, and implementing responsible governance—will be best positioned to thrive in an increasingly intelligent and data-driven global economy.